Managed Darktrace: What Darktrace 7 Means When Delivered by an MSSP
Many organisations adopt Darktrace for its AI-driven threat detection, but technology alone doesn’t determine security outcomes. The real differentiator is how Darktrace is operationalised, monitored, and acted on across multiple customer environments.
That’s where Managed Darktrace becomes critical.

With the release of Darktrace 7, several platform changes materially improve how Darktrace can be delivered as a managed service. From Redsquid’s MSSP perspective, the most valuable aspects of Darktrace 7 are not isolated features, but the way the platform now supports faster investigations, greater consistency, and improved analyst efficiency across multiple customer environments.
“The most valuable aspects of Darktrace 7 are the improvements that directly increase the SOC’s efficiency, and the reduced friction while pivoting through the platform can improve the MTTR across our customers.”
Redsquid SOC Analyst
This is what Darktrace 7 changes and why it matters when Darktrace is delivered as a fully managed service.
Why Managed Darktrace Is Different from “Running the Tool”
Darktrace is often positioned as a self‑learning AI platform that reduces the burden on security teams. In reality, extracting consistent value still depends on skilled analysts, strong investigation workflows, and the ability to respond quickly when something matters.
A Managed Darktrace service bridges that gap by providing:
- Continuous monitoring and triage
- Consistent investigation processes
- Clear, actionable outcomes. Not raw alerts
Darktrace 7 strengthens this delivery model in several important ways.
Enabling Managed Darktrace at Scale with the ActiveAI Security Portal
One of the biggest operational challenges for delivering Managed Darktrace is managing multiple customer environments without introducing friction or delay, especially during high‑priority incidents.
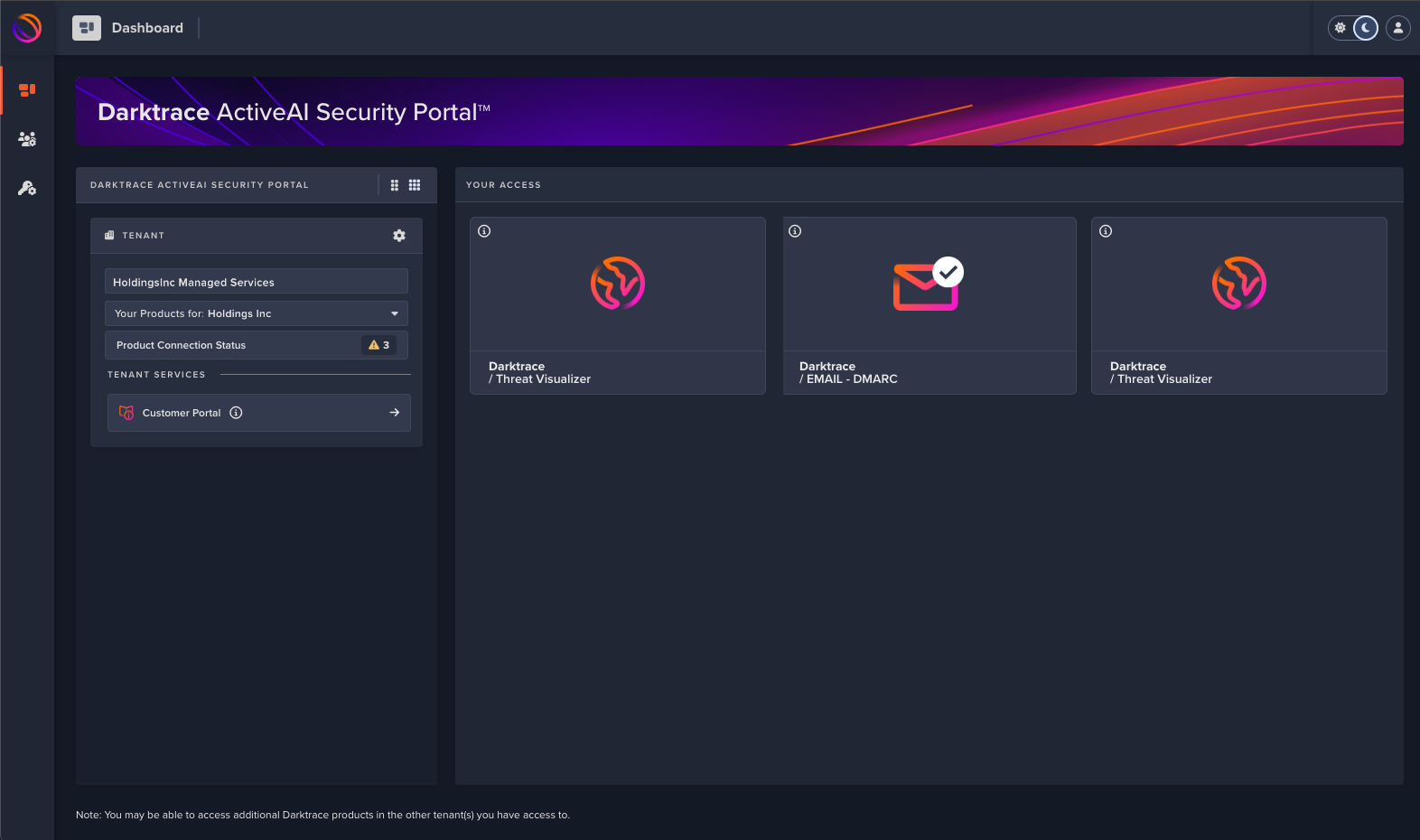
Figure 1: Active AI Security Portal – Centralised access for analysts across multiple Darktrace tenants.
Darktrace 7’s ActiveAI Security Portal represents a meaningful step forward for MSSPs. Centralised, SSO-based access removes the need to maintain local accounts across individual deployments, significantly reducing access management overhead.
For Redsquid analysts delivering Managed Darktrace, this enables:
- Faster pivoting between customer environments
- Cleaner handovers during live incidents
- Simpler onboarding and offboarding
- Stronger governance and access control
These improvements translate directly into faster response times and more consistent service delivery, even as customer numbers and alert volumes increase.
“Centralised access removes unnecessary overhead for analysts and allows faster, cleaner pivoting between customer environments, particularly during high-priority incidents.”
Redsquid SOC Analyst
Process Level Endpoint Visibility:
A Step Change for Managed Darktrace Investigations
One of the most impactful enhancements in Darktrace 7 is the introduction of process-level endpoint visibility.
For Managed Darktrace customers, this addresses a common challenge in investigations. Network-based detections often identify suspicious behaviour, but without endpoint context, validating what actually happened on a host can be slow and disruptive, often requiring customer involvement or additional tooling.
““Process-level telemetry increases our visibility and significantly improves root cause analysis during investigations, without relying on external tooling or customer involvement.”
Redsquid SOC Analyst
With Darktrace 7, Redsquid analysts can correlate network activity with the specific process running on an endpoint, directly within the investigation workflow. This significantly accelerates root cause analysis and improves confidence in decision-making.
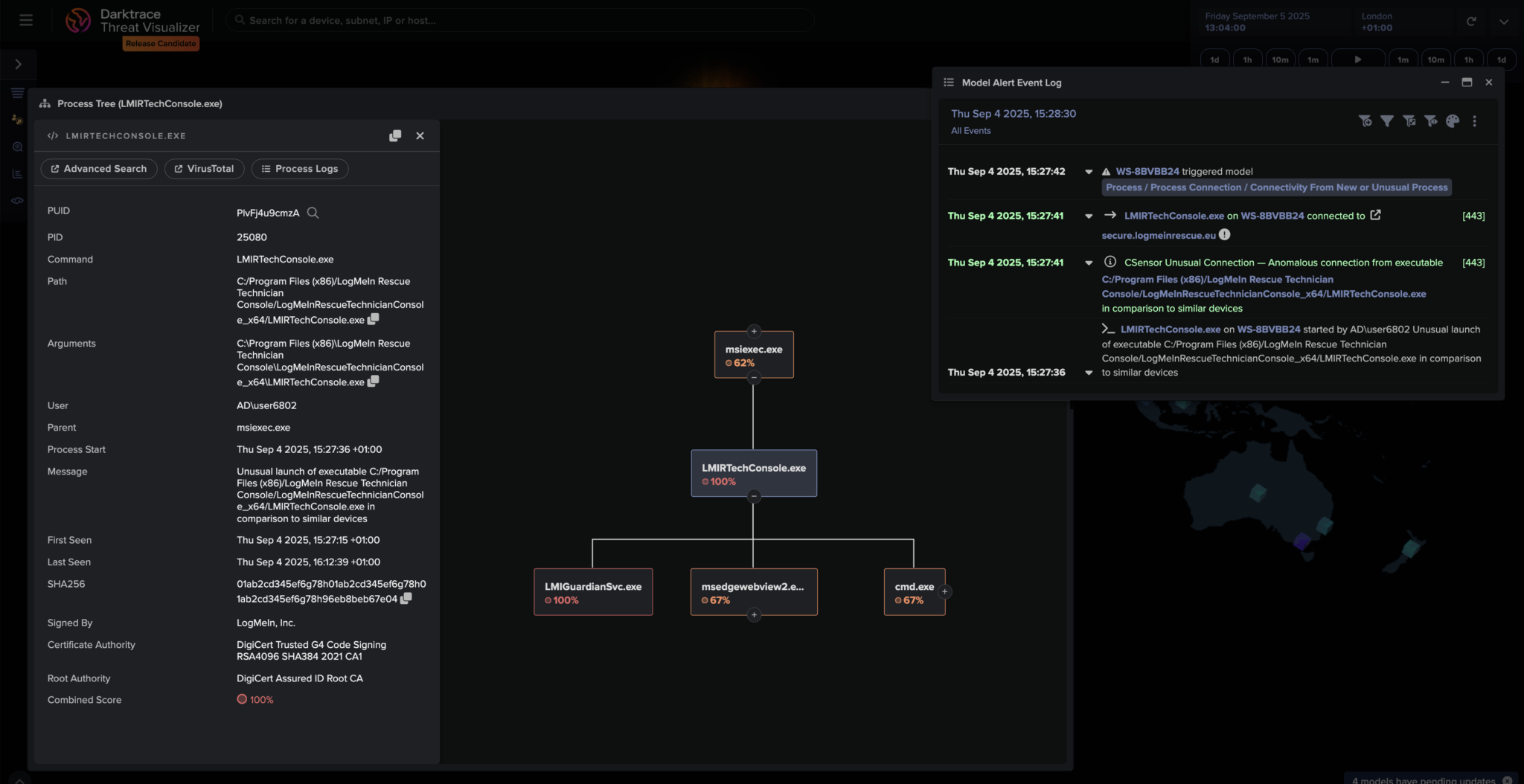
Figure 2: Process-Level Endpoint Visibility – Shows the new process-level telemetry available in Darktrace 7 investigations.
For customers consuming Managed Darktrace, this means:
- Faster answers during incidents
- Less disruption from investigative requests
- Clearer explanations of what occurred and why it matters
Stronger Managed Darktrace Detections Through Endpoint Telemetry
Process-level endpoint telemetry doesn’t just improve investigations. It also enhances detection quality.
Darktrace 7 enables Managed Darktrace services to extend detection logic into endpoint process events. This allows detections to identify which process initiated a connection, rather than relying solely on network behaviour in isolation.
When combined with Darktrace’s behavioural analytics and machine‑learning models, this additional context improves detection fidelity and reduces ambiguity. Analysts gain richer insight into attacker behaviour, enabling more accurate triage and prioritisation.
The result is fewer unclear alerts and faster clarity when a response is genuinely required.
Practical Use Cases: Detecting Unusual Endpoint Behaviour with NEXT
Darktrace 7’s NEXT endpoint capabilities allow Managed Darktrace services to surface behaviour that would be difficult to identify using signatures or static rules alone.
A key use case is the detection of unusual connections from new or unexpected processes. Using Darktrace’s anomaly‑based analysis, Redsquid analysts can identify:
- New processes initiating abnormal external connections, particularly where the destination, protocol, or timing deviates from established device behaviour
- Processes launching from unusual locations, such as user directories or temporary paths, rather than standard install locations
- New or modified scheduled tasks, which may indicate persistence mechanisms being established on an endpoint
Rather than relying on predefined indicators, Darktrace models what is normal for each device and process, allowing genuinely anomalous behaviour to stand out quickly. For a Managed Darktrace SOC, this provides earlier visibility into endpoint‑based attack activity, including living‑off‑the‑land techniques, and enables faster, more confident investigation and response.
Consistent UI: Reducing Friction in Managed Darktrace SOC Operations
Security outcomes are influenced not just by detection capability, but by how efficiently analysts can operate day to day.
Darktrace 7 continues a clear move toward UI standardisation across modules, with increasingly consistent layouts and investigation workflows across Network, Cloud, OT, Endpoint, and Exposure Management.
For a Managed Darktrace SOC, this consistency delivers tangible benefits:
- Reduced cognitive load for analysts
- Faster ramp-up for new team members
- Smoother investigations with less context switching
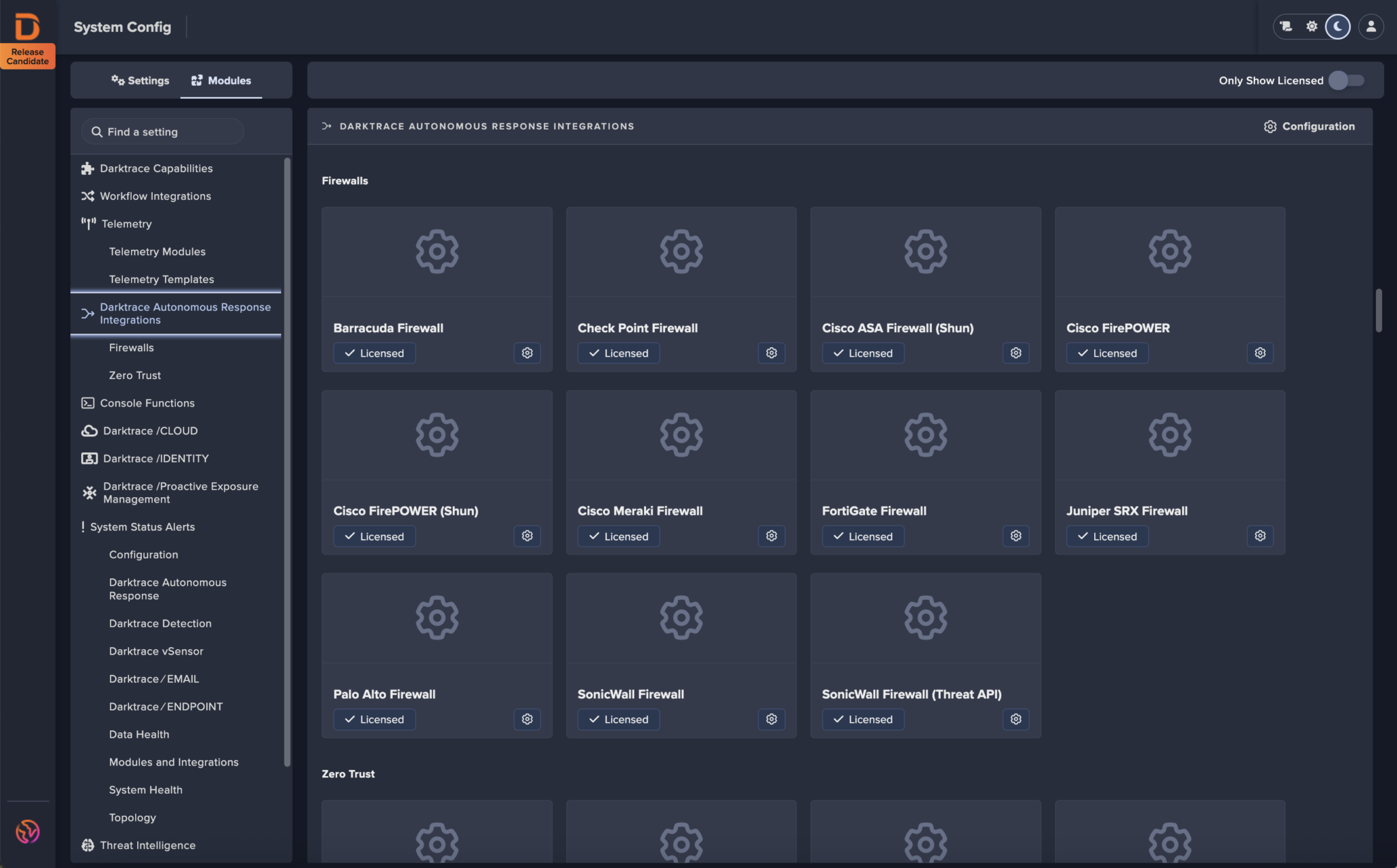
Figure 3: Unified Darktrace UI – Standardised layouts that reduce analyst friction across modules.
For MSSP’s, these incremental gains compound, allowing analysts to manage more investigations concurrently while maintaining quality and speed of response.
What This Means for Managed Darktrace Customers
The value of Darktrace 7 in a Managed Darktrace model isn’t about headline features. It’s about how these changes support a repeatable, scalable, and outcome-driven SOC service.
Collectively, Darktrace 7 enables Managed Darktrace providers to deliver:
- Simpler multi-tenant access that improves analyst agility and governance
- Richer endpoint context that accelerates investigations and root cause analysis
- Consistent workflows that reduce friction, training overhead, and investigation time
These improvements align closely with how Redsquid delivers Managed Darktrace: prioritising speed, clarity, and consistency over raw alert volume or tool complexity.
Managed Darktrace Is About Outcomes, Not Tools
Darktrace provides powerful detection capabilities, but the outcomes customers experience depend on how those capabilities are operationalised.
Darktrace 7 strengthens the foundation for Managed Darktrace services by reducing operational friction and improving investigation quality. When delivered by an experienced MSSP, these improvements translate directly into faster response times, clearer outcomes, and more effective security operations.
For Redsquid, the focus remains the same: delivering Managed Darktrace as a service, not just deploying technology and ensuring customers receive clear, timely, and actionable security outcomes.
Want to understand how Redsquid delivers Managed Darktrace to reduce MTTR and improve SOC performance?
Get in touch with our team to see how Managed Darktrace works in practice.
